Azure Security Technologies
Harden your Azure Platform against security threats
Your most valuable digital assets, namely your database, needs to be protected from both internal, as well as external threats. Securing access to the database lowers the impact of a security breach and loss of data. However, this is not enough.
In addition to securing the operating environment of your database server(s), you will also need to configure networking security, privacy of sensitive data, control access to database objects and much more. SQL Server tools make it possible to create one or more policies and apply these policies across one or more databases.
While SQL Server provides high levels of security out-of-the-box, it is imperative to reduce its attack surface, use secure operations and take measures against threats.
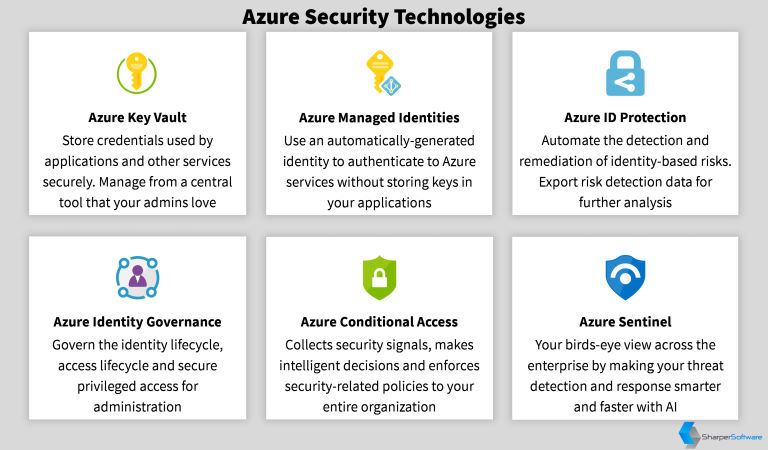
Azure Security Technologies Offered by Sharper Software
Microsoft Azure provides a lot of security technologies. Here's a list of technologies offered by Sharper Software:
| Technology | Capabilities |
|---|---|

|
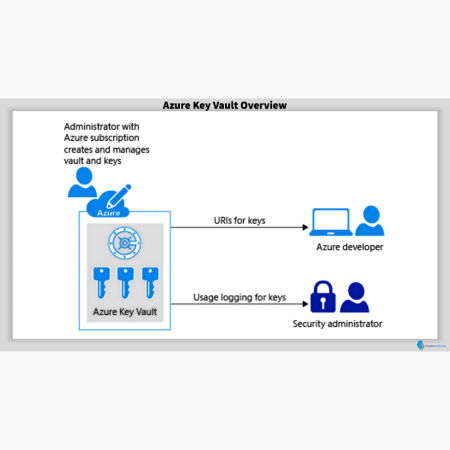
Azure Key Vault
|

|
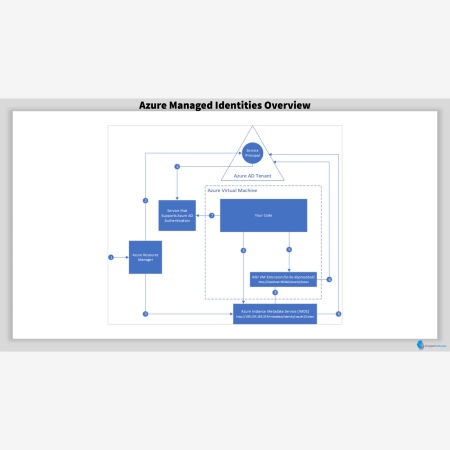
Azure Managed Identities
|

|
Azure Identity Protection
|

|
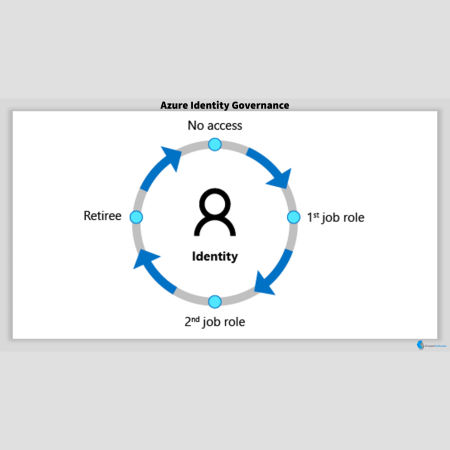
Azure Identity Governance
|

|
Azure Conditional Access
|

|
Azure Sentinel
|
Gallery
Mission-Critical Performance
In-memory operations deliver on average 10x transactional, as well as 100x Data Warehousing performance gains.
Faster Insights
Speed up how you access, analyze, clean and shape data. Turn meaningless data into decision-making information.
Platform for Hybrid Cloud
Work with your data in a hybrid environment that spans on-premises to the cloud. Use any combination of both scenarios.
All Built-in
Use Integration Services, Reporting Services, Analysis Services, Data Quality Services, Master Data Services, etc.
Significant Cost Savings
SQL Server has a Total Cost of Ownership of 1/10 of Oracle. This gives you significant savings.
You are the champion!
You are at the center of attention. By meeting and possibly exceeding your expectations, you become a champion.