SQL Server Hardening Services
Harden your SQL Server instances against security threats
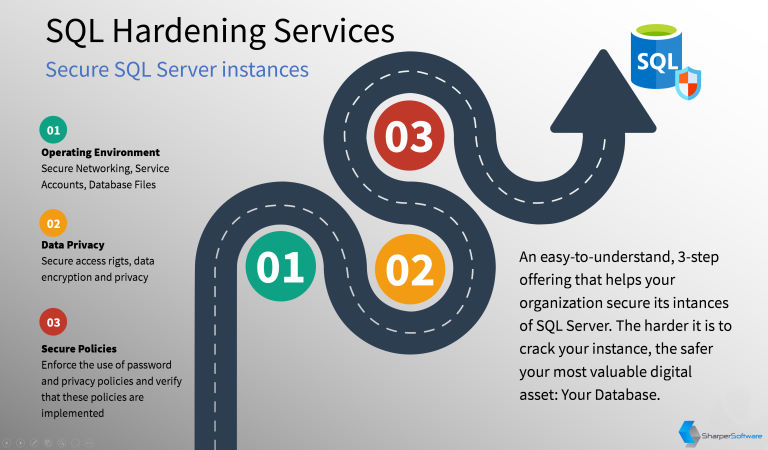
Your most valuable digital assets, namely your database, needs to be protected from both internal, as well as external threats. Securing access to the database lowers the impact of a security breach and loss of data. However, this is not enough.
In addition to securing the operating environment of your database server(s), you will also need to configure networking security, privacy of sensitive data, control access to database objects and much more. SQL Server tools make it possible to create one or more policies and apply these policies across one or more databases.
While SQL Server provides high levels of security out-of-the-box, it is imperative to reduce its attack surface, use secure operations and take measures against threats.
SQL Server Hardening Approach
Sharper Software provides an easy-to-understand, 3-step approach to harden your instances of SQL Server:
-
Operating Environment.We secure the operating environment of your SQL Server instance(s) by:
- Securing the network protocols used by SQL Server services. Only required services will be configured and the rest will be disabled.
- Domain Service Accounts will be used to run the SQL Server services instead of local accounts. The 'sa' account will be disabled and a Domain Security Group will be used.
- Furthermore, the database files will be encrypted with asymmetrical keys in order to avoid data leaks outside the organization.
-
Data Privacy. We take data privacy seriously:
- Users will be provided access to SQL Server using a least-privileged policy. Users shall have access only to those database objects they need and no others.
- Domain accounts will be used instead of SQL Server accounts where possible.
- If an application is used to manage user privileges, an application account will be used instead of individual user accounts.
- If a web-based application is used, the user account and password used to access the underlying database will be securely stored in the IIS Application Pool account. This makes hacking the database connected string very difficult.
-
Secure Policies. Now that the attack surface is reduced, it is imperative that security issues do not repeat
themselves in the future.
- We will enforce the use of secure password policies on your Domain as well as SQL Server instances.
- We will design secure policies with the presence of your resources, implement these policies and use tools to occasionally verify that these policies have not been violated.
Gallery
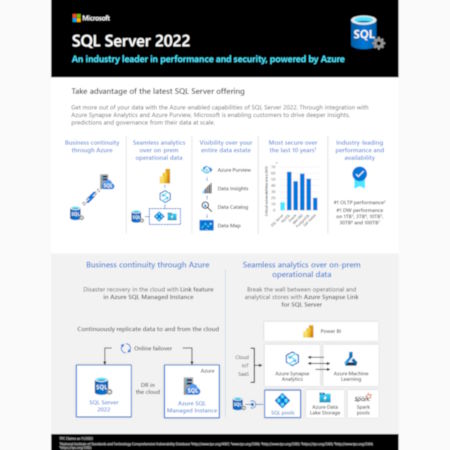
Mission-Critical Performance
In-memory operations deliver on average 10x transactional, as well as 100x Data Warehousing performance gains.
Faster Insights
Speed up how you access, analyze, clean and shape data. Turn meaningless data into decision-making information.
Platform for Hybrid Cloud
Work with your data in a hybrid environment that spans on-premises to the cloud. Use any combination of both scenarios.
All Built-in
Use Integration Services, Reporting Services, Analysis Services, Data Quality Services, Master Data Services, etc.
Significant Cost Savings
SQL Server has a Total Cost of Ownership of 1/10 of Oracle. This gives you significant savings.
You are the champion!
You are at the center of attention. By meeting and possibly exceeding your expectations, you become a champion.